A massive supply chain attack hit the VoIP communication company, 3CX, on Wednesday evening. The attack involved distributing Windows applications containing Trojan malware. The attackers exploited a vulnerability in the Windows system that has been around for a decade, and to make matters worse, Microsoft removed the patch for this vulnerability in its Win11 system. The hackers replaced two DLL files used by the Windows desktop application(Windows Vulnerabilities), and once the device runs this malicious application, it will download other malicious software such as information-stealing Trojans.
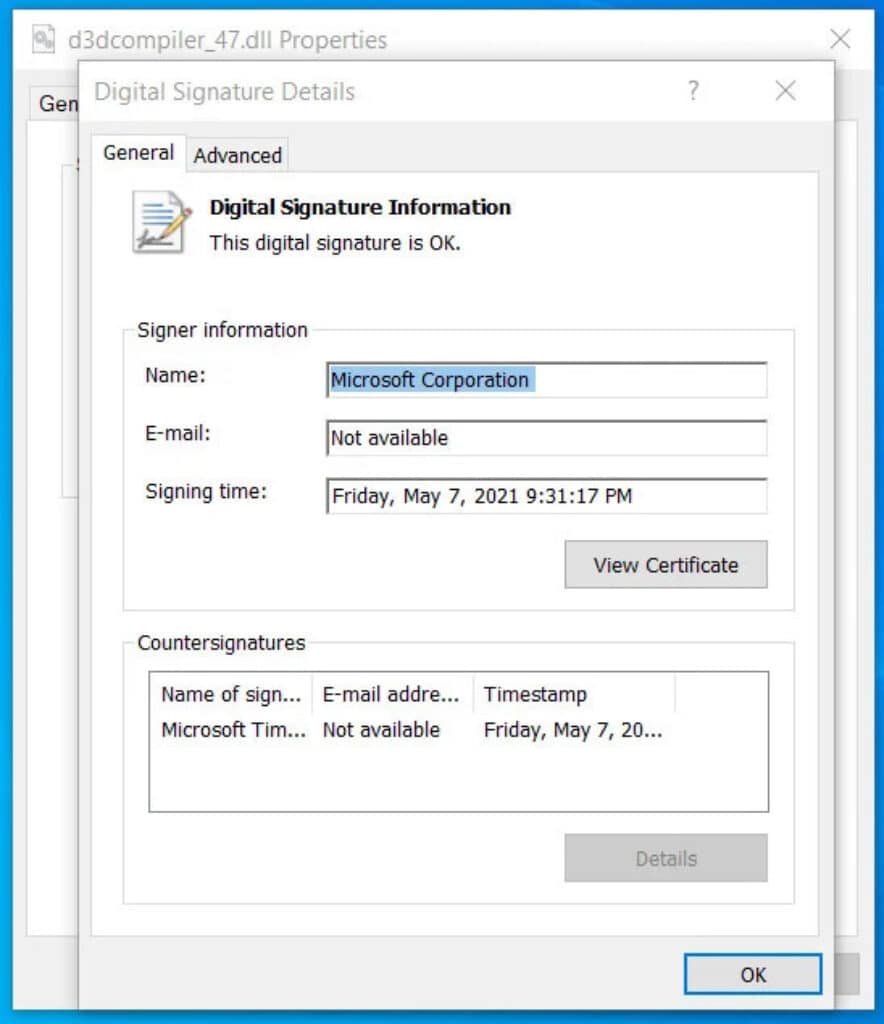
According to Gizcoupon’s report, one of the DLL files is a legitimate DLL signed by Microsoft, named d3dcompiler_47.dll. The hackers modified this DLL to include an encrypted malicious payload at the end of the file. When the device runs this malicious software, the Windows system still shows that it is officially signed by Microsoft.
The attack on 3CX highlights the vulnerabilities and risks of supply chain attacks. In fact, supply chain attacks have become increasingly common and pose a significant threat to businesses, organizations, and governments worldwide. As a result, hackers often target a company’s suppliers or partners to gain access to the company’s systems, data, and networks.
Read More: Lenovo’s Savior 9000X with Wi-Fi 7
Keeping software and systems updated with security patches is crucial. Also, using trustworthy partners is essential. The 3CX attack should warn other companies to review their security protocols and ensure protection.
3CX posted a security advisory, advising users to update and add security measures after the attack. Customers and partners were notified and advised to take precautions.